- Home
- Security Testing
Security Testing Services

Companies work with various programs and services that contain and process the personal data of customers and employees. They try to protect their information systems in many ways, including network security, passwords, authentication, anti-virus protection, etc. However, no security systems can guarantee complete reliability against hacker attacks.
Therefore, mobile security testing, web app security testing, and web security testing are mandatory steps in any IT project. This process helps identify weaknesses in information systems that can be exploited to access data or steal confidential information and assess the level of data protection against three critical security aspects - confidentiality, integrity, and data availability.
Software Security Testing Services
Our team currently provides various manual and automated security testing services, each with its benefits and areas covered.
Security Audit
It is a method of testing the system by QA analysts for compliance with safety standards and regulations to protect against external and internal threats, which helps to identify weaknesses in security policies and processes and make recommendations for improvement. It includes document analysis, staff interviews, system testing, risk assessment, and report of findings and proposals.
Risk assessment
Using this quality control method, QA engineers analyze the potential risks and threats of the system. They then develop mitigation strategies and measures to assess and prioritize remedial action. This process may include identifying assets, vulnerabilities, threats, and controls, analyzing the impact of activities, calculating risk levels, and developing a risk mitigation plan.
Security Awareness Training
Information security training is a type of education aimed at increasing the knowledge and skills of employees, IT professionals, and other stakeholders on how to protect themselves and their organizations from cyber threats.
Penetration Testing
With this method, QA engineers conduct a detailed analysis of the network and systems from the point of view of a potential attacker. They simulate cyberattacks to identify security weaknesses, which helps assess risk and improve application resilience against real threats. The essence of the check is an authorized attempt to circumvent the existing protection of information systems. As a result, using different methods and tools, we can determine how mechanisms respond to intrusion.
Vulnerability assessment
This method is aimed at finding and eliminating gaps in the system by QA specialists, through which an attacker can penetrate and steal critical data. It consists of scanning the system with special programs, checking code or settings manually, prioritizing vulnerabilities, and developing a plan to eliminate or mitigate them. This approach makes the system more secure and protected from attacks.
Tools we use
Maltego
Shodan
BurpSuite
OWASP
Nmap
nessus
OpenVAS
metasploit
What Do We Test
Our experienced Luxe Quality team will analyze and determine the security of your product to do everything possible to ensure the reliability, availability, and protection of your service. We offer you software security testing of your technologies from different perspectives:
Network services
Servers
Firewalls, IDS/PSs and other security solutions
Application protocol interfaces (APIs)
Frond end and back end of applications
Benefits of Regular security testing
Regular security testing gives you many positive results, such as:
Vulnerability Remediation
Find and fix weaknesses in your applications, systems, and networks that could be a target for cybercriminals or hackers.
Risk Mitigation
Assess and mitigate security risks that result in data loss or reputational damage as a result of security breaches.
Compliance Analysis
Analysis of compliance with the standards and security requirements of your industry or organization.
Trust Enhancement
Strengthening the trust and loyalty of your users and partners in your products and services protected from vulnerabilities.
Quality Improvement
Improving the quality and efficiency of software, provided that security testing is included in the development process.
Why choose Luxe quality for your security testing
Security Expertise
Luxe Quality has a team of engineers who have deep knowledge and skills in the field of information security and conduct testing according to the best practices and industry standards such as OWASP, NIST, ISO, and others.
Professional Partnership
By choosing Luxe Quality as your business partner, you get a professional, high-quality, and efficient service to help you protect your application or software from potential threats or attacks.
Customized Service
We always adapt our services to the needs and requirements of each client, taking into account the specifics of the business, application, and software, as well as its goals and expectations from security testing.
Comprehensive Testing
A complete cycle of testing is provided for your project, including threat and risk analysis, vulnerability testing, penetration testing, code and infrastructure security testing, security auditing, and security improvement consulting.
40 hours of free testing
Luxe Quality has a special offer tailored for potential long-term customers who are interested in starting a pilot project.
We are offering our software testing and QA for free for the first 40 hours.
Luxe Quality Security Testing process
Analyzing
Analyzing security requirements and risks to set testing goals and priorities.
Planning
Planning security testing using the IEEE 829 standard to prepare a document that contains the purpose, priorities, procedures, and impact of security testing.
Choosing methods for testing
Choosing methods and tools for security testing depends on the type and features of the software. For example, vulnerability scanning, penetration testing, security auditing, etc.
Performing security testing
Performing security testing using selected methods and tools to detect and assess application, system, and network vulnerabilities.
Documenting and reporting
Documenting and reporting the results of security testing, indicating the vulnerabilities found, risks, and recommendations for their elimination or mitigation.
Сontrol
Сontrol the correction of vulnerabilities or the implementation of compensatory controls to increase software security testing.
Cooperation Models Luxe Quality Offers
Luxe Quality offers two security control options:
One-Time security Testing
This is a one-time security check of your application before launch or update, in which QA specialists analyze requests and responses between different parts of your application and look for vulnerabilities. The purpose of such testing is not only the detection of errors and defects but also an assessment of the protection of your application at the time of testing.
Continuous security testing
It is the process of checking for security vulnerabilities in web applications and IT infrastructure on an ongoing basis. Continuous security testing integrates security tools and practices into the DevOps pipeline so that security checks are performed automatically at every software development and delivery stage. Ongoing support includes re-testing after eliminating threats and vulnerabilities found earlier.
Case studies
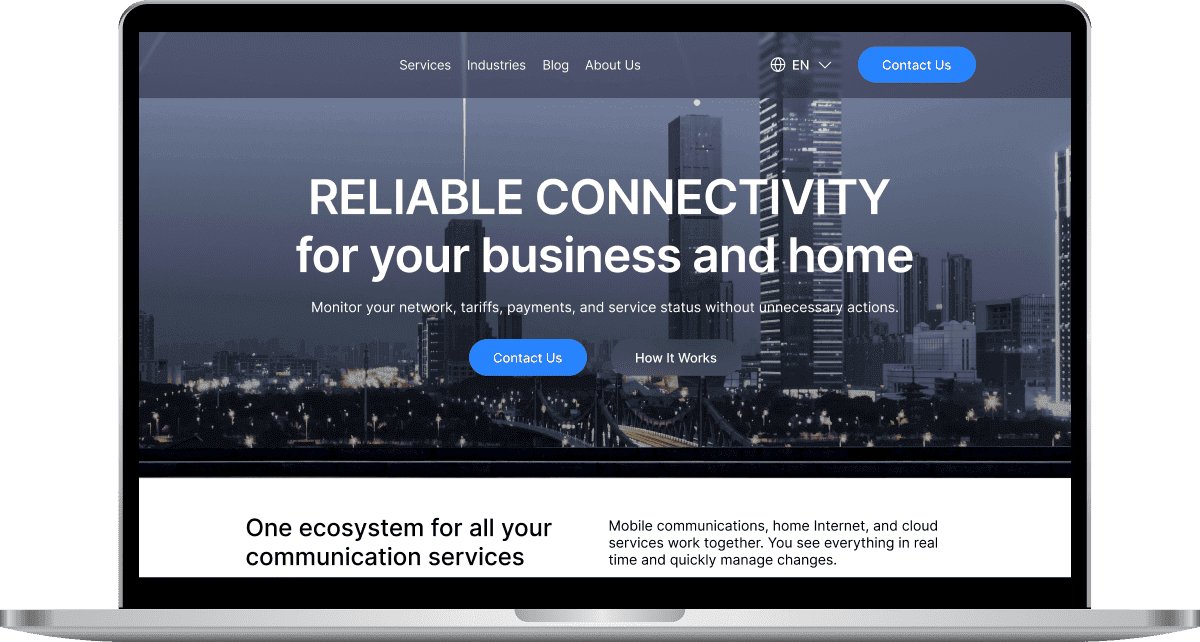
More projectsDigital Connectivity Company
USA
•Web, Mobile
About project:
A digital connectivity company offering mobile, internet, and digital communication services.
Services:
- Manual and Automated testing, API, Security, Usability, Cross-browser, Cross-platform testing
- Automated testing -TypeScript + WebdriverIO + Mocha + Appium
Result:
350+ automated regression tests integrated into the CI/CD pipeline, ~50% fewer complaints from clients to support.FULL CASE STUDY
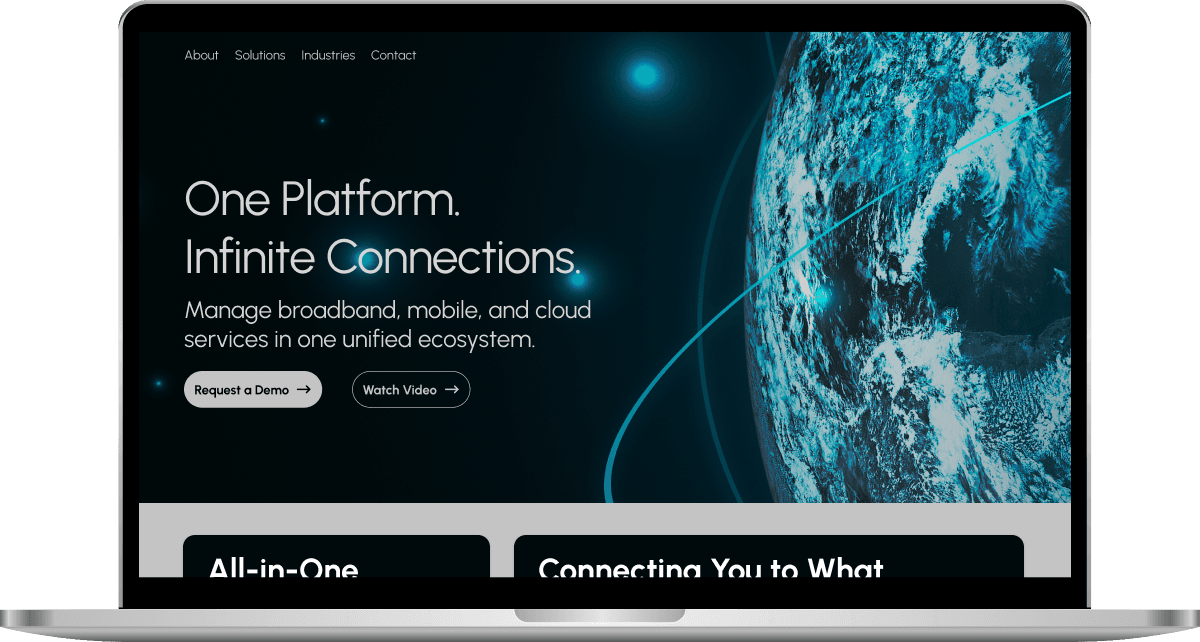
Telecommunications Provider
USA
•Web, Mobile
About project:
The client is a telecommunications provider offering broadband, mobile, and cloud communication services.
Services:
- Manual and Automated testing, API, Smoke, Regression, Performance, Security, Usability, Cross-platform testing
- Automated testing -TypeScript + WebdriverIO + Mocha + Appium
Result:
~70% of regression tests automated, reducing manual QA's involvement in regression cycles by 60%.FULL CASE STUDY
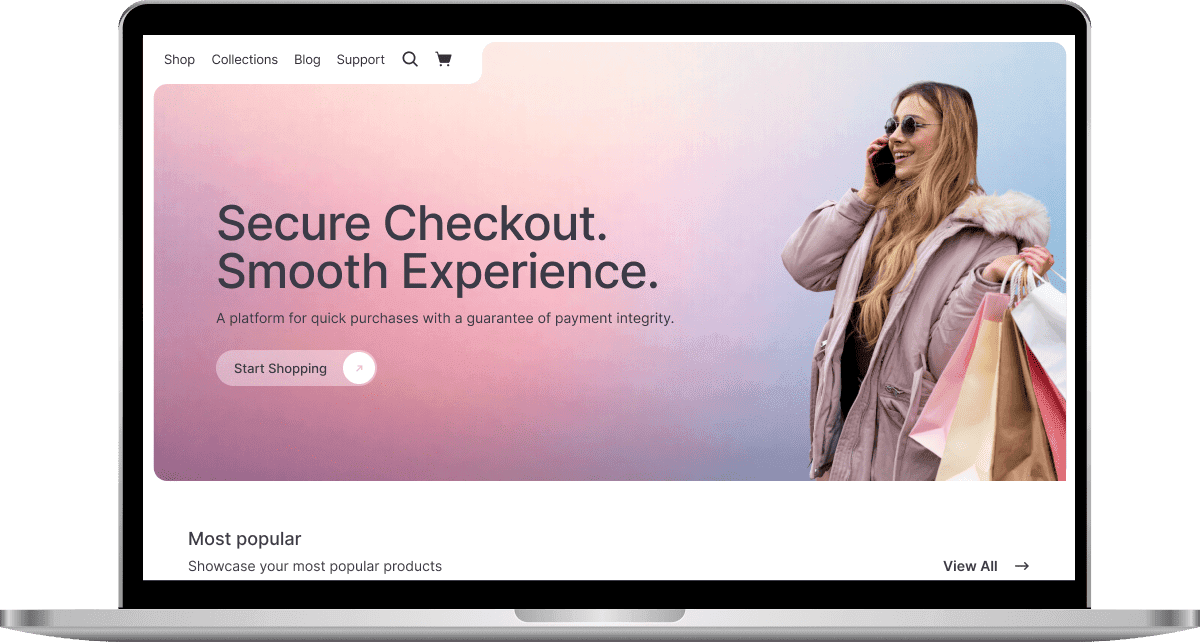
E-Commerce Retailer
USA
•Web, Mobile
About project:
An online E-commerce retailer that provides customers with a seamless online shopping experience through its web and mobile platforms.
Services:
- Manual and Automated testing, API, Usability, Cross-browser, Cross-platform testing
- Automated testing -TypeScript + WebdriverIO + Mocha + Appium
Result:
~80% drop in user-reported issues, critical checkout errors reduced to near zero, predictable, on-time releases for all major updates.FULL CASE STUDY


Our Clients Say
Get in touch
Our workflow
Now: Just fill out our quick form with your project details. It’s easy and only takes a minute.
In a Few Hours: We’ll assess your information and quickly assign a dedicated team member to follow up, no matter where you are. We work across time zones to ensure prompt service.
In 1 Day: Schedule a detailed discussion to explore how our services can be tailored to fit your unique needs.
Following Days: Expect exceptional support as our skilled QA team gets involved, bringing precision and quality control to your project right from the start.
FAQ
QA specialists conduct security testing of a system or application to identify weaknesses, threats, and possible security problems and their subsequent elimination.
Security testing helps to identify gaps, threats, and risks in an application or system that attackers can exploit. Also, check for compliance with industry norms and standards to keep important information safe and sound. A security breach is a loss of reputation, money, and users.
A security audit thoroughly reviews an organization's information systems by comparing them against criteria such as rules or standards. It aims to identify weaknesses and, as a result, gives recommendations on ways and methods to improve the system's security in the future. The audit allows you to assess the security status at each technical level of the project.
This is an essential step in information security management, which consists in identifying and assessing potential threats to the organization's information resources. A risk assessment helps you determine how likely and severe a security breach or data loss might be due to these threats. Risk assessment aims to rank risks according to their degree of criticality and find effective measures to reduce or eliminate them. The process includes identifying assets, threats, vulnerabilities, probabilities, impacts, and control methods.
Pentesting tests the security of computer systems, networks, or web applications by simulating attacks by malicious actors. It helps to assess the security level of a system and recommend measures to improve it.